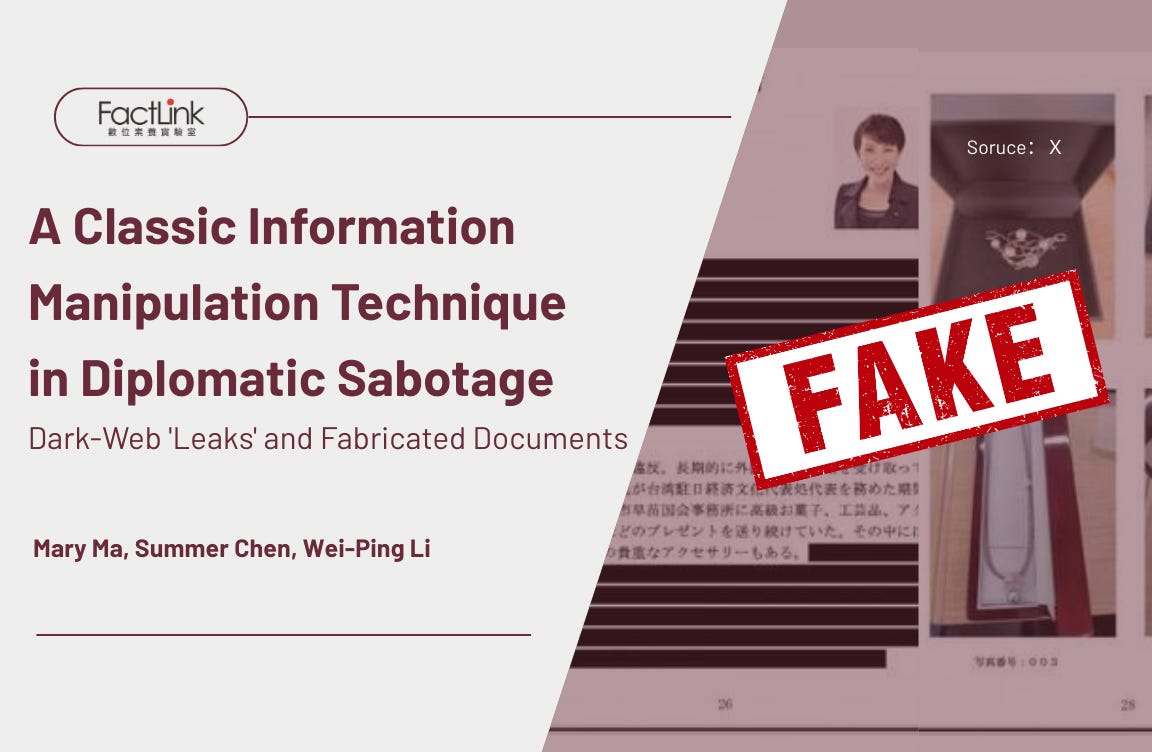
A Classic Information Manipulation Technique in Diplomatic Sabotage: Dark-Web 'Leaks' and Fabricated Documents
Feb 22, 2026
Authors: Mary Ma, Summer Chen, Wei-Ping Li
Data support: FIMI Intelligence Dashboard by Doublethink Lab
One of the most notable cases among the Chinese Communist Party (CCP)’s information manipulation campaigns responding to Japanese Prime Minister Sanae Takaichi’s statement that “China’s attack on Taiwan could constitute an existential crisis for Japan” (hereafter referred to as the “Taiwan contingency statement”) was the disinformation involving a fake “document leak” claimed to provide “evidence” of “Taiwan’s jewelry bribery to Japan.”
Recently, the technique of leaking “classified diplomatic documents via the dark-web” has been used to manipulate information and erode societal trust during significant political moments. Perpetrators imitate hackers by staging a “hack and leak” operation, posting false documents on anonymous forums. They then disseminate these fake documents and posts through the media and social platforms to simulate a genuine leak. This strategy often targets Taiwan during diplomatic advances, aiming to tarnish its success by suggesting it was bought or bribed, thereby questioning the legitimacy of Taiwan’s diplomatic accomplishments.
Following Takaichi’s “Taiwan contingency statement” in the Japanese parliament, a similar information manipulation strategy reemerged: malicious actors fabricated a hacking and leakage incident by disseminating forged documents, aiming to depict Taiwan-Japan relations as “bribery diplomacy.” This effort seeks to defame Taiwan and Japan’s mutual support and undermine Takaichi’s stance on Taiwanese affairs.
Notably, in this “Jewelry Gate” fake document incident, one can observe multiple online accounts, directly or indirectly linked to the CCP, as well as social media pages highly aligned with the CCP’s narratives, and Hong Kong media with close CCP ties, amplifying the disinformation. This kind of aggressive amplification was very different from the strategies seen in previous attacks against Taiwan, in which manipulators and amplifiers sought to hide their connections to the CCP. Furthermore, after Taiwanese fact-checking reports and media coverage revealed the manipulation, some malicious accounts quickly deleted their posts, suggesting this might be a coordinated operation warranting further investigation.
FactLink has identified four defining characteristics of this type of information manipulation.
Feature 1: Two Waves of Coordinated Attacks
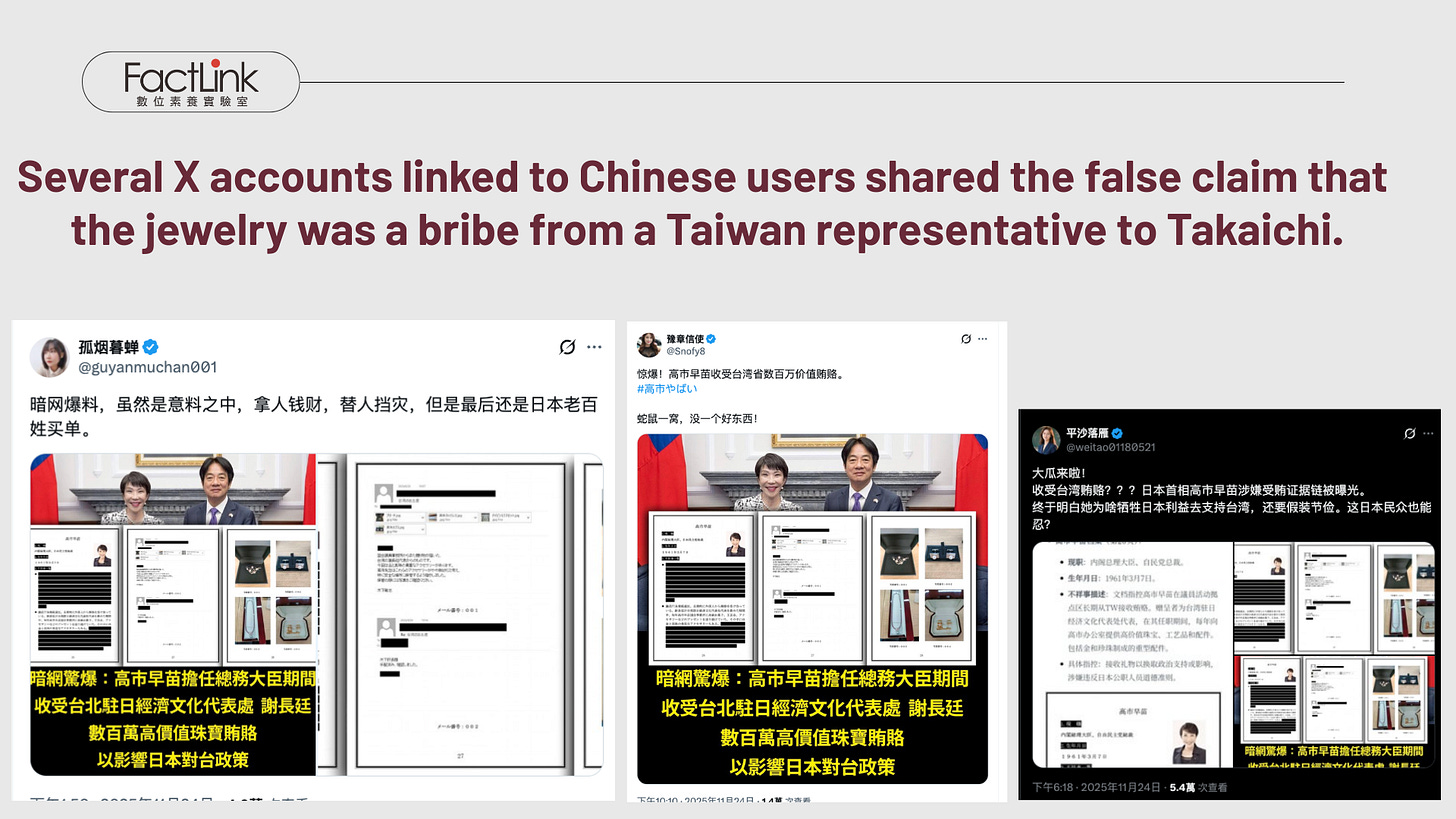
On November 24, 2025, multiple online accounts and fan pages across various platforms simultaneously shared similar messages. For instance, a Facebook page called “Taiwan Internet Window[台灣網路視窗],” a Chinese-language X account named “Lonely Smoke Dusk Cicada[孤烟暮蝉],” which mainly posts political comments, and another pro-CCP Chinese X account “Yuzhang Messenger[豫章信使],” which has frequently been flagged by fact-checkers for spreading false information, all circulated the claim: “Dark-web bombshell: While serving as Minister of Internal Affairs and Communications, Sanae Takaichi accepted millions of yen in high-value bribes from Taiwan’s representative to Japan, Hsieh Chang-ting of the Taipei Economic and Cultural Representative Office, to influence Taiwan-Japan policy.”
These posts included what appeared to be correspondence records between Japanese parliament members and photos of jewelry. The Taiwan FactCheck Center quickly identified this rumor as disinformation on November 25, 2025. According to the fact-check report, one clear sign of the documents’ falsehood was that, although the letters purported to be correspondence between Takaichi and parliamentary staff, the Japanese language used was inappropriate and full of mistakes.
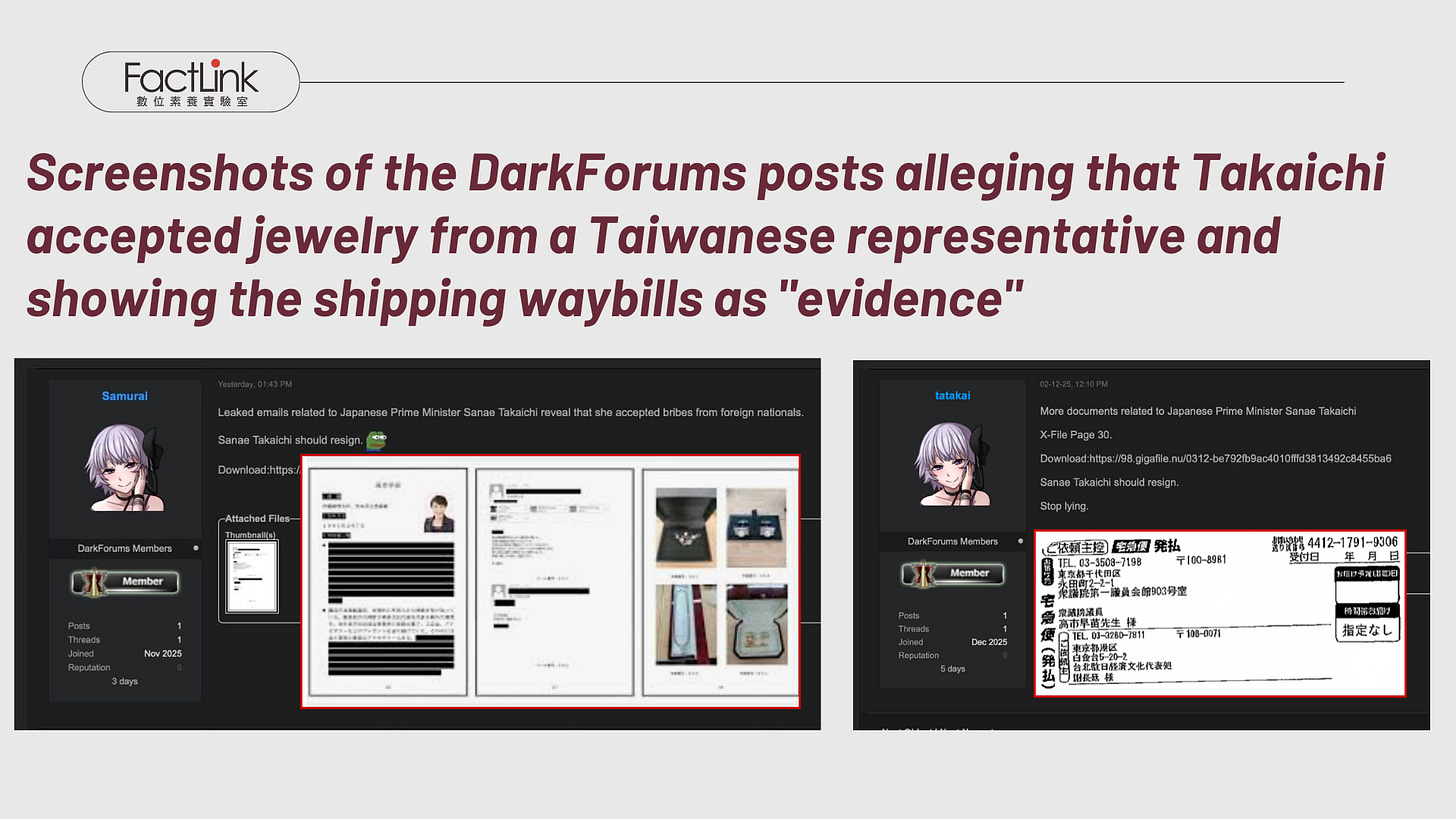
An investigation into the source of the leaked content also revealed that the so-called “dark-web bombshell” mentioned by these accounts actually originated from the anonymous forum “DarkForums,” rather than a real dark-web site. An account named “Samurai,” which was newly created on November 23, initially posted this false Taiwan-Japan diplomatic document on the same day as the account was created.
Nevertheless, even though Taiwanese media, fact-checking organizations, and the accused himself, Hsieh Chang-ting, made clarifications, the wave of information attacks persisted.
On December 2, 2025, another user on the same forum, “tatakai,” published more so-called “X-Files” that showed “shipping waybills for jewelry transported in Japan to Takaichi” as supposed proof of Takaichi’s involvement in bribery. The post also called for her resignation for hiding the fact that she had accepted a bribe.
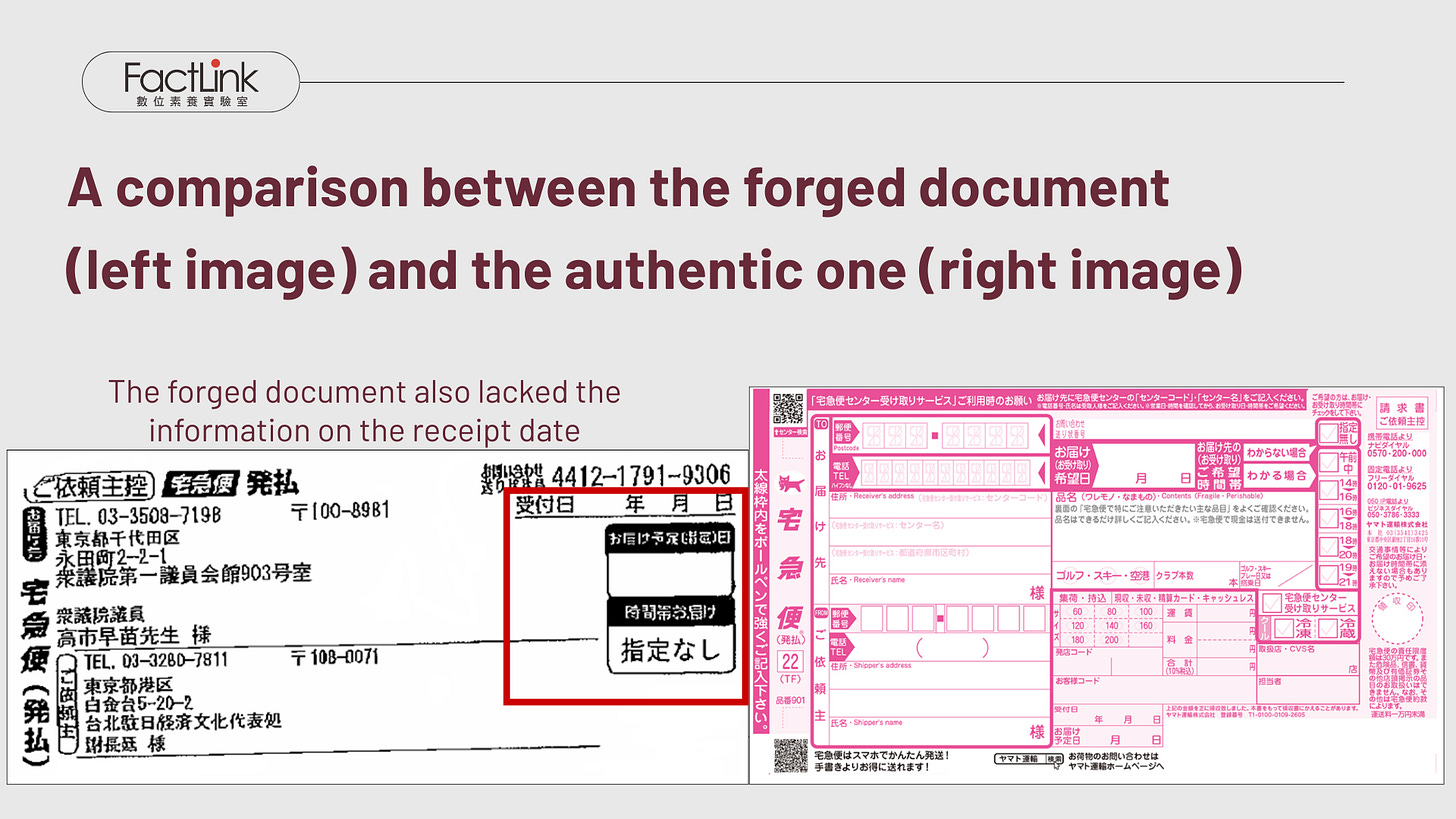
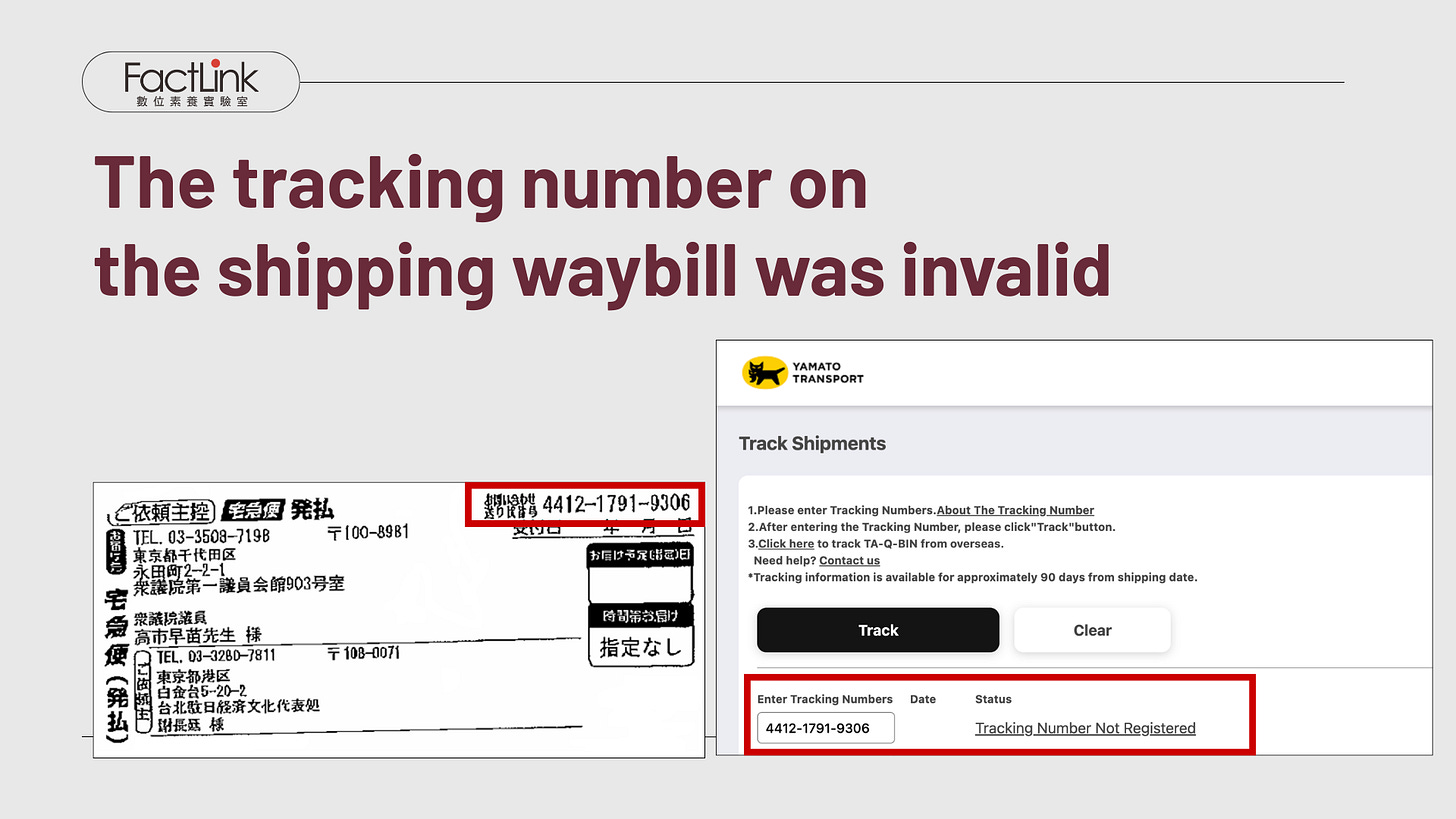
FactLink verified that the shipping waybill was not an official Yamato Transport (YAMATO) document since it lacked a shipping date. Besides, a search for the listed tracking number returned no results in Japan’s official logistics system, indicating that the document was forged.
Feature 2: An Information Manipulation Attack Simulating “Hack and Leak” Technique
Huang Li-an, an analyst at the Cyber-threat intelligence company Team T5, observed that this “faked dark web leak of documents” was a hybrid information manipulation strategy intended to mimic a hack-and-leak incident.
Huang explained that a traditional “hack and leak” cybersecurity attack involves a malicious actor infiltrating a government or organization’s system, stealing authentic and sensitive data, and then publicly releasing it to influence public opinion or achieve specific political goals.
This technique often occurs during election cycles. For example, in the 2016 U.S. presidential election, Russian hackers accessed Democratic Party emails to expose Hillary Clinton’s campaign strategies. In 2024, Iranian actors infiltrated Trump campaign documents and leaked them to the media.
As for the “DarkForums” involved in this incident, where the documents appeared to be leaked, the forums cannot be accessed through regular search engines; users need a specific link to access them. The malicious actors thus claimed the documents as a “dark web leak” to create the impression that “the data comes from hackers,” thereby boosting the documents’ credibility.
However, according to Huang, since the documents posted on DarkForums were fabricated rather than actual documents that were leaked, this incident cannot be classified as a typical hack-and-leak operation. Instead, the entire incident was just a staged one aiming to make an impression that the bribery incident was true.
FactLink has also noted that this type of attack has occurred not only during elections but also during Taiwan’s diplomatic milestones. These include U.S. House Speaker Pelosi’s visit to Taiwan in 2022, President Tsai Ing-wen’s diplomatic visits to Central and South American countries in 2023, and then-Vice President Lai Ching-te’s trip to Paraguay in 2023. In each case, a pattern of “dark-web leak + forged document” attacks was observed, aiming to tarnish Taiwan’s diplomacy as “money diplomacy.”
Feature 3: The Four-Stage Smear Campaign — Baiting, Transporting, Landing, and Amplifying — with Chinese-user Accounts Coordinately Spreading the Attack
As FactLink has observed several information manipulation cases attacking Taiwan in recent years, FactLink has found that this type of information manipulation follows a distinctive propagation pattern, which can be divided into four stages: “baiting, transporting, landing, and amplifying.”
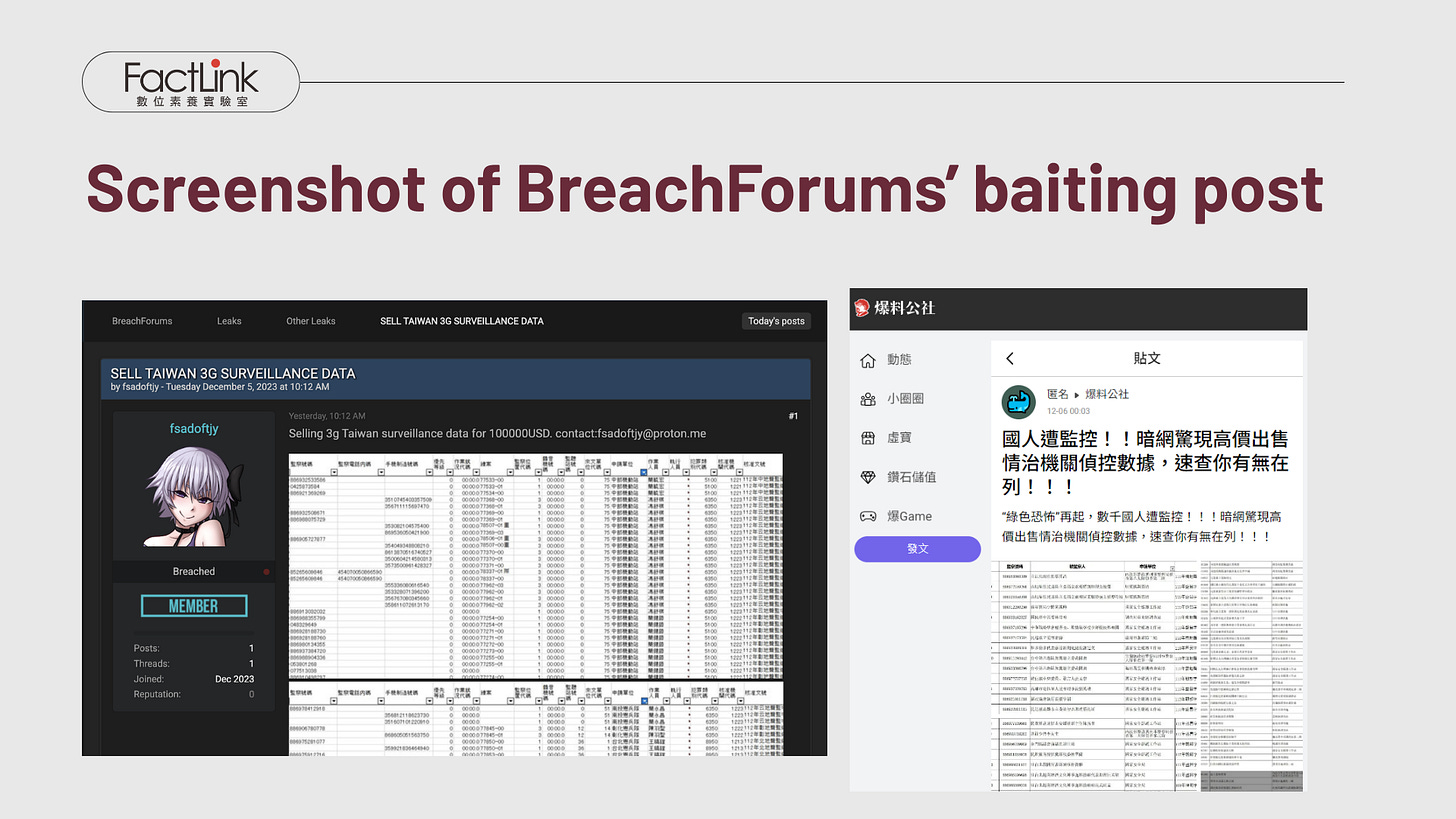
An example is the incident involving “intelligence agency surveillance data on the dark web,” which emerged just before Taiwan’s 2024 presidential election. On December 6, 2023, the Taiwanese online forum “Baoliao Gongshe [爆料公社]” claimed that a leaked dark web document indicated the DPP government was surveilling citizens and enforcing a “Green Terror.” This document was initially posted as “bait” on “Breach Forums” on December 5, then shared on Baoliao Gongshe, catching the attention of Taiwanese media and netizens. The media and online users picked up the bait, spreading it into public media spaces. As a result, the false message “landed” in mainstream media as well as social media and was further amplified.
During the “transporting,” “landing,” and “amplifying” phases, the strategy often leverages commentators who make sensational claims to garner media attention — sometimes leading the targeted parties or organizations to respond with denials and clarifications. In a media environment where true and false information coexist and spread together, once a rumor moves from online comments to a public debate, causing doubt about the targeted party, the objective of information manipulation is effectively accomplished.
Comparing the “dark-web leak + forged document” attacks used against Taiwan and Japan, there are notable differences. Huang Li-an says, “The Jewelry Case also utilized the technique of fake information combined with dark web leaks — but unlike previous cases, this time we observe a far larger volume of Chinese accounts participating in the spread.”
Examining the propagation path of the “fake Jewelry documents” incident, the campaign began with baiting on DarkForums, but during the transporting and amplifying stages, multiple X platform Chinese accounts with a history of spreading pro-China narratives and disinformation, such as “Yuzhang Messenger,” “Lonely Smoke Dusk Cicada,” and “Flat Sand Falling Geese,” as well as China’s NetEase platform, simultaneously joined in spreading the content.
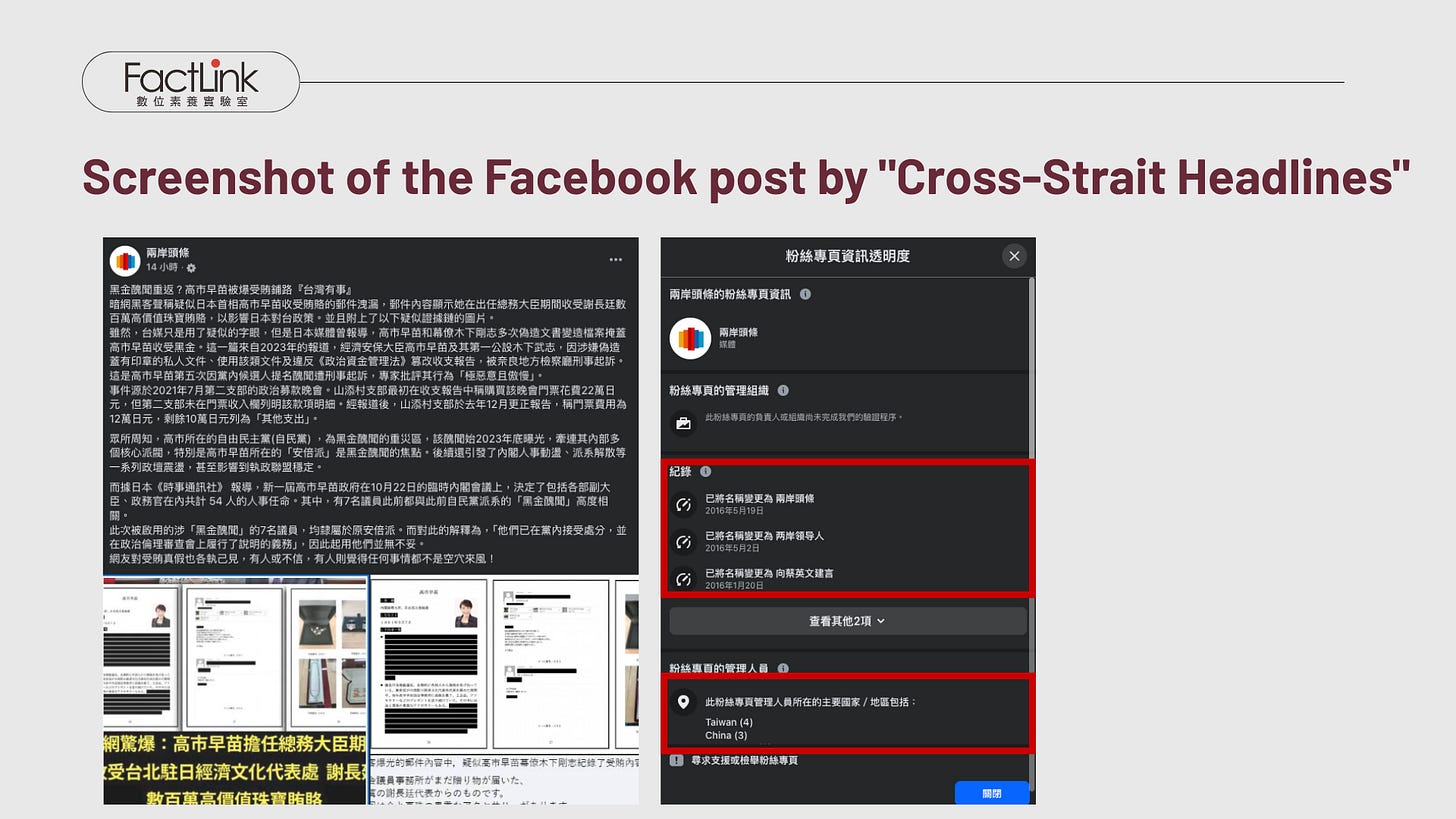
Furthermore, the Facebook page “Cross-Strait Headlines [兩岸頭條],” which is closely connected to the CCP, along with the Hong Kong newspaper Wen Wei Po [文匯報], also circulated the same content. However, once Taiwan exposed the rumor as false information, both “Cross-Strait Headlines” and Wen Wei Po promptly removed and deleted their posts.
“Cross-Strait Headlines” has a history of spreading pro-China disinformation. A search of its contact details and email shows it is a Facebook page operated by the Hong Kong pro-China media outlet “Chinavtv [中华微视].” The page has changed its name several times and has administrators based in both Taiwan and China.
When comparing attack strategies against Taiwan and Japan, malicious actors spreading disinformation aimed at Taiwan tend to avoid using accounts tied to Chinese networks. FactLink’s research team believes that Taiwan’s longstanding efforts in media literacy and fact-checking have increased public awareness of “disinformation launched by China,” leading information manipulators to become more covert and hide their sources. Nonetheless, in the “Jewelry Diplomacy” disinformation case, a noticeable China-related propagation chain was clearly identified. This difference underscores the importance of further investigation.
Feature 4: The “Bribery/Money Diplomacy” Narrative
Throughout the entire information manipulation process of this “Jewerly gate”, the central theme is the “Taiwan-Japan bribery diplomacy,” with “dark-web leak” acting as the primary “weapon” to initiate the attack. This “dark-web leak” narrative also establishes a “technical barrier,” making it challenging for downstream media outlets to verify the claims and for the public to distinguish between truth and falsehood.
An analysis of content spread by these CCP-linked actors uncovers narratives like “bribery diplomacy,” “bought and paid for,” and “corrupt at every turn,” all aimed at damaging Taiwan-Japan diplomatic ties. This technique exploits existing public skepticism in Taiwan about monetary diplomacy to criticize the Taiwanese government and diplomatic agencies. At the same time, it tarnishes Takaichi’s reputation by calling her “corrupt,” challenging the legitimacy of her diplomatic stance on Taiwan.
FactLink notes that fake documents claiming to expose “diplomatic secrets” and circulating on the so-called dark-web often contain disinformation. By framing these online posts and documents as “exclusive exposés,” the false narratives divert attention from crucial diplomatic issues and instead smear and attack individual politicians.
Huang Li-an also warns that, with public trust in traditional media decreasing, information leaked through so-called dark-web revelations tends to draw more public interest and can more readily give rise to conspiracy theories, increasing their spread.
Defense Strategies Against “dark-web leak + forged document”
Taiwan has faced several incidents involving “dark-web leak + forged documents” during diplomatic breakthroughs and elections. In this case, as the CCP responded to Takaichi’s “Taiwan contingency statement,” malicious actors employed the same technique: posting seemingly “leaked classified documents” on the dark-web, waiting for mainstream media or social media users to pick them up unwittingly. What sets the “Taiwan contingency statement” case apart is that the actors were transparent about their links to the CCP and appeared to coordinate different groups to carry out the propaganda campaign.
In Taiwan, these attacks frequently claim to expose secrets related to diplomacy, national security, history, or personal matters. This approach hampers outsiders’ ability to quickly collect comprehensive information for accurate judgments. It also makes verification and fact-checking more difficult, leading the media to publish rushed reports and fueling public division. As a result, these attacks particularly test the skills of media gatekeepers and fact-checkers, as well as the public’s digital literacy.
Institutions combating information manipulation should urgently reassess past cybersecurity incidents, develop verification protocols, and establish cooperation frameworks among organizations across various media outlets. They should also leverage these cases to develop journalist training and media literacy initiatives to strengthen information resilience.
Furthermore, Taiwan and Japan can share experiences and analyze research findings on propaganda techniques, networks, and narratives across events to develop strategies for strengthening information resilience.